Few have dared to attempt the mammoth task that is pioneering digital asset insurance. Put off by a market that still finds itself in its early days, insurance professionals will often shy away from the topic for fear of having their lack of understanding exposed. But the world of digital assets – cryptocurrency, e-commerce, social media, and gaming – is becoming increasingly integral to our personal and commercial lives, demanding, in turn, a greater understanding of the cyber risks they carry. Our community of cyber insurance professionals tuned in to hear Rafael Broshi, CEO of Notch Insurance, explain how his MGA handles digital asset cyber risk with their innovative product.
Want to watch the full Masterclass on Digital Asset Insurance? Enter your details here to recieve a free recording.
What Are Digital Assets?
A digital asset is anything intangible that has either a universal or specific value to its holder.
For example, one Bitcoin could have a universal, monetary value of $15,000-$20,000; similarly, an asset like a Twitter account with a significant following could hold monetary value if it acts as a major marketing tool or distribution channel which generates sales elsewhere.
On the other hand, a Whatsapp or email domain may theoretically have negligent monetary value, but it could hold immense personal or specific value to its holder. The personal value of a digital asset can be substantial. For example, a significant following on a social media account indirectly provides its holder with social standing, reputation, and credibility. Likewise, many people rely on social media accounts to communicate with others.
Key Risks Affecting Digital Assets
Theft
This can arise through the following attack methods:
- Data leaks: Leaked personal information can often end up on the Dark Web and be purchased by threat actors to steal several digital assets at once. This is especially common if the same credentials are used for different digital assets and multi-factor or two-factor authentication is not set up.
- Social engineering: This attack method, which includes phishing, is commonly used to steal crypto, social media accounts, and e-commerce stores.
- Brute force attacks: These are less common because most digital platforms that house digital assets have defenses in place against brute force attacks (for example, social media platforms will often lock a user out of an account if the wrong password is inserted five times in a row).
Loss
Holders of digital assets can lose their assets if they:
- Forgetting or losing their password and being subsequently locked out: This is especially likely to happen if the holder has not updated the phone number and email address associated with the asset. The issue is exacerbated when a user is locked of their account on a platform that is heavily used in everyone’s day-to-day, such as Facebook, Google or Instagram. With so many users, it is extremely difficult for support teams to verify the rightful owner of locked accounts.
- Violating a platform’s Terms of Service (‘ToS’): This may result in a ban from accessing and using the platform. For businesses that rely on these platforms as their main distribution channel, this can be particularly problematic.
- Are mistakenly banned by the platform’s algorithm: Algorithms are commonly used by digital platforms to verify accounts on a pre-programmed basis. Those accounts that the algorithm considers violate its ToS may be automatically banned. Issues can arise with hyper-sensitive algorithms: the tighter and stricter the thresholds programmed into the algorithm, the higher the chance of an account being mistakenly banned.
Digital Asset Hack: Case Study
A notable cyber event concerning the popular social media platform, Twitter, in 2020 highlighted the danger of social engineering attacks on holders of digital assets. A company investigation found that several employees had been subject to a coordinated social engineering attack which enabled their access to internal systems to be compromised. The threat actors then used Twitter’s internal systems to leverage the large following of high-profile Twitter accounts to dupe other Twitter users into parting with Cryptocurrency. Although the breach was shortly detected and contained, over $300,000 was made by the hackers from crypto payments made by innocent Twitter users.

Digital Asset Insurance Is Not A One-Size-Fits-All Product
Similarly to fine art insurance, a well-underwritten digital asset policy will be highly individualized to meet the unique characteristics of the asset in question and will include a full suite of protections, specific to that asset.
The nature, frequency, and severity of cyber risks that insurers must consider in a digital asset insurance policy vary according to the digital assets in question. Rather than simply classing assets into categories and issuing blanket policies per class, underwriting digital asset insurance must take into account the specific details of each asset, such as the platform on which the asset sits, the size of the asset’s following, or the strength of engagement with that asset. For example, a YouTube account with a high number of views may cost more to insure than a Twitter account with fewer followers. Therefore, the underwriting process must be tailored to each individual asset, even if they are within the same class of assets.
Additionally, the coverage offered for each digital asset should be tailored to the specific needs of that asset. For example, a cryptocurrency may only require coverage for the monetary value of the asset, while a full suite of services may be necessary for a social media account. It is important to consider the unique characteristics of each digital asset and provide coverage accordingly.
What Does Digital Asset Insurance Need to Cover?
In recent years, cyber insurance underwriting has placed greater emphasis on the entire chain of events involved in a cyber event. Accordingly, both crisis management services and proactive risk management feature heavily in today’s cyber policies; cyber insurance is no longer a “bandaid to heal all”, rather, it must be used in conjunction with exceptional cyber hygiene best practices. Given the rapid pace of change in the digital asset arena, digital asset insurance policies are likely to adopt a similar focus on proactive risk management.
Incident Prevention
One of the main cyber-related challenges facing the digital asset space involves social engineering attacks, which are difficult to fend off through traditional cyber security means (i.e. tools and technological defenses). Therefore, a large part of proactive risk management associated with digital assets should involve the promotion of best practices. Armed with better education on key risks at hand, holders of digital assets can take smarter steps to minimize their exposure.
Payouts
Even with high levels of cyber hygiene, the possibility of a cyber threat actor succeeding in executing an attack can never be zero. In such an eventuality, digital asset insurance protects against the potential fallout of a catastrophic cyber event.
The impact of such an event can vary depending on the nature of the affected asset. For instance, the loss of a social media account that is used as a distribution channel for a business can result in a range of consequences, including the loss of valuable data, the need for public relations management, and future earning potential for a business. In some cases, compromised accounts can be used by attackers to scam others, further multiplying the indirect losses stemming from the initial attack. This makes it difficult to know the full extent of the damage caused by a cyber event and to determine the appropriate payout for a digital asset insurance claim. Conversely, the direct loss of the monetary value of a digital asset would be the primary concern surrounding a crypto hack and can be more easily calculated.
Therefore underwriters must consider the asset in question when calculating its insurance policy’s limits, coverages, and exclusions.
Notch’s policy does not include risks like platform downtime, which reduces the accumulation of risk to low-frequency business interruptions. This allows Notch to use a semi-parametric model that combines automated onboarding, monitoring, and payment with semi-automated underwriting and adjudication.
Cyber insurance may not fully cover social media, even if it is an insured’s digital storefront
Cyber policies will generally cover the digital asset (such as an Instagram handle or a YouTube account name) that is listed on the policy’s declarations page. This means that cyber insurance policies will typically cover a takeover of a social media account but there are some important limitations in cyber policy coverage, which Notch’s product is designed to answer.
Many modern-day businesses, particularly those operating in the e-Commerce sector, will rely on their social media accounts as key distribution channels: in these business models, the content published on social media ultimately directs consumer traffic to the Point of Sale (the business’ website).
Limited access to these social media accounts can therefore prompt major business interruption as website traffic and sales decline suddenly and consumers flock to competing businesses.
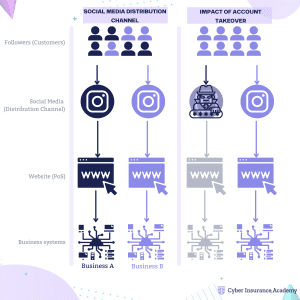
Where a social media account is lost or stolen, but a website is still running, the holder of the digital asset may not be entitled to make a claim for lost profit as a result of business interruption. Notch’s digital asset insurance policy is designed to address this gap in coverage by protecting micro and small businesses that generate income directly or indirectly through their social media accounts.
Crisis Management
The type of post-incident support provided by digital asset insurance will depend on the specific coverage agreed upon, which will in turn depend on the asset in question. In some cases, this support may include services such as account retrieval, public relations management, or assistance in rebuilding a business from scratch.
As more and more transactions, records, and other valuable information are stored digitally, the potential for loss or damage to these assets is growing. Insurance professionals who are knowledgeable about digital assets will be able to better assess the risks associated with them and provide appropriate coverage to their clients. In addition, understanding digital assets will help insurance professionals stay current with industry trends and remain competitive in a rapidly changing marketplace.
Want to watch the full Masterclass? Enter your details here to recieve a free recording.