What is the Dark Web
The Dark web is accessed via a dedicated browser, the most common of which is Tor. These browsers are built on what is called the “onion router”, so-called because it comprises a complex, multi-layered network. It is these layers that enable the high levels of encryption and anonymity that many surfers on the Darknet are after.
The Dark web’s URL structure is unconventional as it is typically longer than the URLs commonly come across on browsers such as Google or Chrome, and it is formatted with a mix of numbers and letters. This naming structure increases the difficulty of keeping track of activities on the Dark web. Ultimately, Dark web users must be absolutely resolute in what they are searching for in order to actually find it. Otherwise, they will need an invitation from someone who is already “on the inside”.
The key advantage of the Dark web is that it enables anonymous communication between users. The IP addresses that identify Dark web users change rapidly, meaning that by the time the IP address is successfully traced through, it is no longer in use. It is for this reason that so many criminal minds have gravitated towards the Dark Web as a place to make bank, and it has therefore garnered a reputation as a criminal underground network for highly illegal activities.
The rise of cryptocurrency has also boosted activity on the Dark web. While fiat currencies are still used on this part of the internet, cryptocurrencies are extremely popular as they provide a convenient method of hiding the identities and transaction details of the people using them.
You can find a recording of her masterclass here.
Where is the Dark Web?
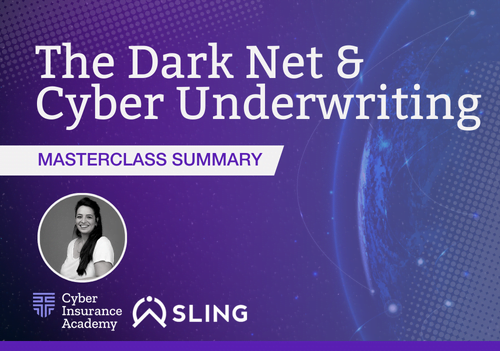
The browsers we typically use to access a website, such as Google or Bing, form what is known as the Surface Web. These browsers index the content of websites across the Internet so that those websites can appear in search engine results.
But the surface web is considered to comprise only 5% of the entire internet. This means that the vast majority of content on the internet is not indexed and is therefore not easily discoverable. This information, such as personal banking accounts or healthcare accounts, is found on what is known as the Deep Web and lies behind closed doors.
Within the Deep Web is the Dark Web. To continue with the door analogy – this part of this internet can only be accessed by very specific doors, and they will lead to very specific rooms, but all fall under the same roof of the Internet.
Anything-and-Everything-as-a-Service
The Dark web is a vast virtual space – and it is growing. Whilst it is not illegal to browse the Dark web, its content can be problematic. It is the home of anything and everything – from ISIS recruiters to drugs and so much more. There has subsequently been increased monitoring of the Dark web by law enforcement organizations and cyber intelligence experts, and it is therefore slightly less discreet today than it once was.
The Dark Web can be considered as an Anything-as-a-Service (or XaaS) marketplace for business owners of all shapes and sizes, whether criminal or otherwise. “XaaS” conveys a general category of services related to cloud computing and remote access. It recognizes the vast number of products, tools, and technologies that are now delivered to users as a service over the internet.
Financial Motivation & DarkWeb Threat Actors
A cyber threat actor is a state, group, or individual which might maliciously intend to exploit technological and cyber security vulnerabilities in an organization to gain unauthorized access to its information systems. There are different categories of threat actors, which you can read about in our guide.
The most common threat actors on the Dark web are those motivated by financial gain. The Dark Web is their marketplace. Governmental agencies and intelligence experts keep this incentive in mind when trying to identify or locate cyber criminals because money is often more easily traceable than humans behind encrypted IP addresses. By applying basic commercial acumen to follow the proceeds of crime, the criminal benefitting from it can sometimes be tracked down.
Monetizing the Dark Web Kill Chain
This is where Yuval brought the Darknet to life with a step-by-step demonstration of how this monetization looks – watch her recording here for a truly immersive experience.
The Threat Model
What has emerged in the Dark Web is a structure of highly specialized cybercriminals, each with their own niche skills, expertise, and offering to meet the various stages of a successful cyber-attack and to cash in on the proceeds. In brief, these stages include:
- Recon (Reconnaissance). This is the process of collecting technical information about a cyber target, such as mapping out an organization’s digital assets, including the number of domains and the types of technologies that it employs.
- Weaponization. This is where the data collected is used to identify potential vulnerabilities or entry points in the organization.
- Delivery. Here, an attacker infiltrates the organization by exploiting the vulnerability identified in Phase 2.
- Exploitation. This is where, for example, a hacker will install malware, extract and encrypt data or carry out some other form of attack
What we see on the Dark Web is that each stage of this threat model is commercialized separately, and often by different criminals. Each criminal utilizes their own skill within the threat model, operating as a separate business. Ultimately, a Dark Web shopper may well find that they need to employ the services of 4 different cyber criminals in order to execute one successful attack on a target company. Because of this high level of monetization, intelligence analysts can apply their own commercial awareness and business savvy, consider the threat actors’ motivations and follow the money through these stages to the end of the cyber “kill chain”. Once intent can be identified, and once the threat model is considered, deriving conclusions is much easier.
The Business Model
There are several potential monetization channels for threat actors to choose from on the Dark Web. These channels all have one thing in common: they all rely on a compromised machine. From that point on, a threat actor can monetize, for example, Private Identification Information (PII) to execute identify theft; or they can leverage a compromised website to spread malware through spam; they can also package and sell access to an organization’s network to ransomware affiliates.
In the case of network access, the Dark Web can be used for several different commercial opportunities pertaining to a single attack alone. Once the threat actor has successfully compromised a corporate network, access to that network can be advertised and traded on the Dark Net Market. Then, by cooperating with other attackers with access to a ransomware source code, that network access can be commercialized. Finally, the network access is monetized with a large ransom demanded of the victim.
The Automated Model
In keeping with general global trends, the Dark web is shifting away from its traditional, service-orientated markets (with different factions in the cybercrime underground specializing in particular niches) and towards automation. Under this new model, an automated escrow can be created and goods can be instantly delivered to the customer who purchased them. This is likely to present a good opportunity for intelligence collection.
The Dark web and its clandestine reputation have often been approached with timid apprehension. However, the reality is that this slice of the internet holds very little dark mystery. The motivations behind the illicit activities on this part of the Net often carry an underlying, financial logic that can be mapped, understood, and pursued, with monetization ending the cybercrime kill chain more often than not.
With thanks to Yuval Sapir for her insight. You can find a recording of her masterclass here.